Download Certified Ethical Hacker v13.312-50v13.ExamTopics.2026-04-01.293q.tqb
| Vendor: | ECCouncil |
| Exam Code: | 312-50v13 |
| Exam Name: | Certified Ethical Hacker v13 |
| Date: | Apr 01, 2026 |
| File Size: | 1 MB |
How to open TQB files?
Files with TQB (Taurus Question Bank) extension can be opened by Taurus Exam Studio.
Purchase
Coupon: TAURUSSIM_20OFF
Discount: 20%
Demo Questions
Question 1
Harris is attempting to identify the OS running on his target machine. He inspected the initial TTL in the IP header and the related TCP window size and obtained the following results:
TTL: 64 -
Window Size: 5840 -
What the OS running on the target machine?
- Windows OS
- Mac OS
- Linux OS
- Solaris OS
Correct answer: C
Question 2
Emily, an extrovert obsessed with social media, posts a large amount of private information, photographs, and location tags of recently visited places. Realizing this, James, a professional hacker, targets Emily and her acquaintances, conducts a location search to detect their geolocation by using an automated tool, and gathers information to perform other sophisticated attacks.
What is the tool employed by James in the above scenario?
- ophcrack
- VisualRoute
- Hootsuite
- HULK
Correct answer: C
Question 3
As a certified ethical hacker, you are performing a system hacking process for a company that is suspicious about its security system. You found that the company’s passwords are all known words, but not in the dictionary. You know that one employee always changes the password by just adding some numbers to the old password. Which attack is most likely to succeed in this scenario?
- Brute-Force Attack
- Password Spraying Attack
- Hybrid Attack
- Rule-based Attack
Correct answer: C
Question 4
A multinational corporation's computer system was infiltrated by an advanced persistent threat (APT). During forensic analysis, it was discovered that the malware was utilizing a blend of two highly sophisticated techniques to stay undetected and continue its operations.
Firstly, the malware was embedding its harmful code into the actual binary or executable part of genuine system files rather than appending or prepending itself to the files. This made it exceptionally difficult to detect and eradicate, as doing so risked damaging the system files themselves.
Secondly, the malware exhibited characteristics of a type of malware that changes its code as it propagates, making signature-based detection approaches nearly impossible.
On top of these, the malware maintained a persistent presence by installing itself in the registry, making it able to survive system reboots.
Given these distinctive characteristics, which two types of malware techniques does this malware most closely embody?
- Polymorphic and Metamorphic malware
- Polymorphic and Macro malware
- Macro and Rootkit malware
- Metamorphic and Rootkit malware
Correct answer: A
Question 5
A large e-commerce organization is planning to implement a vulnerability assessment solution to enhance its security posture. They require a solution that imitates the outside view of attackers, performs well-organized inference-based testing, scans automatically against continuously updated databases, and supports multiple networks. Given these requirements, which type of vulnerability assessment solution would be most appropriate?
- Inference-based assessment solution
- Tree-based assessment approach
- Product-based solution installed on a private network
- Service-based solution offered by an auditing firm
Correct answer: D
Question 6
Bobby, an attacker, targeted a user and decided to hijack and intercept all their wireless communications. He installed a fake communication tower between two authentic endpoints to mislead the victim. Bobby used this virtual tower to interrupt the data transmission between the user and real tower, attempting to hijack an active session. Upon receiving the user’s request, Bobby manipulated the traffic with the virtual tower and redirected the victim to a malicious website.
What is the attack performed by Bobby in the above scenario?
- aLTEr attack
- Jamming signal attack
- Wardriving
- KRACK attack
Correct answer: A
Question 7
Robin, a professional hacker, targeted an organization’s network to sniff all the traffic. During this process, Robin plugged in a rogue switch to an unused port in the LAN with a priority lower than any other switch in the network so that he could make it a root bridge that will later allow him to sniff all the traffic in the network. What is the attack performed by Robin in the above scenario?
- ARP spoofing attack
- STP attack
- DNS poisoning attack
- VLAN hopping attack
Correct answer: B
Question 8
Taylor, a security professional, uses a tool to monitor her company’s website, analyze the website’s traffic, and track the geographical location of the users visiting the company’s website.
Which of the following tools did Taylor employ in the above scenario?
- Webroot
- Web-Stat
- WebSite-Watcher
- WAFW00F
Correct answer: B
Question 9
You are a cybersecurity professional managing cryptographic systems for a global corporation. The company uses a mix of Elliptic Curve Cryptography (ECC) for key exchange and symmetric encryption algorithms for data encryption. The time complexity of ECC key pair generation is O(n^3), where 'n' is the size of the key. An advanced threat actor group has a quantum computer that can potentially break ECC with a time complexity of O((log n)^2). Given that the ECC key size is 'n=512' and varying symmetric encryption algorithms and key sizes, which scenario would provide the best balance of security and performance?
- Data encryption with AES-128: Provides moderate security and fast encryption, offering a balance between the two.
- Data encryption with AES-256: Provides high security with better performance than 3DES, but not as fast as other AES key sizes.
- Data encryption with 3DES using a 168-bit key: Offers high security but slower performance due to 3DES's inherent inefficiencies.
- Data encryption with Blowfish using a 448-bit key: Offers high security but potential compatibility issues due to Blowfish's less widespread use.
Correct answer: B
Question 10
Security administrator John Smith has noticed abnormal amounts of traffic coming from local computers at night. Upon reviewing, he finds that user data have been exfiltrated by an attacker. AV tools are unable to find any malicious software, and the IDS/IPS has not reported on any non-whitelisted programs.
What type of malware did the attacker use to bypass the company’s application whitelisting?
- File-less malware
- Zero-day malware
- Phishing malware
- Logic bomb malware
Correct answer: B
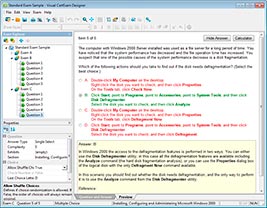
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files
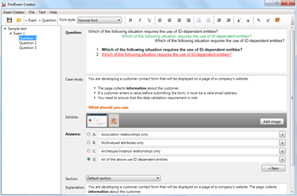
HOW TO OPEN VCEX FILES
Use ProfExam Simulator to open VCEX files
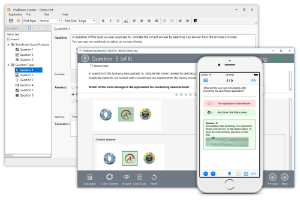
ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



